Real-Time Threat Intelligence: Best Practices
Real-time threat intelligence is reshaping how organizations defend against cyberattacks. Unlike traditional security methods, which rely on periodic scans, this approach works in seconds to detect and respond to threats. Here's why it matters:
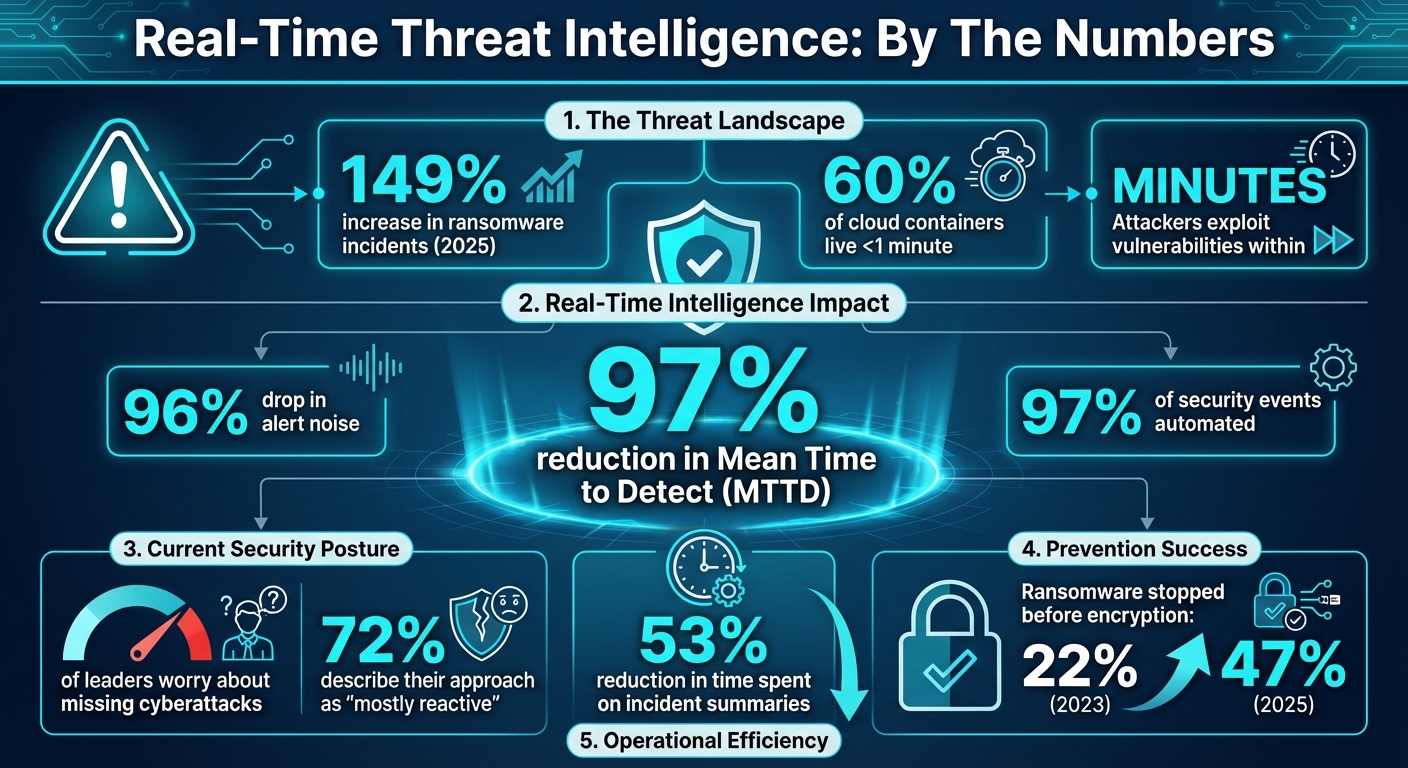
- Speed of Attacks: In 2025, ransomware incidents grew by 149%, with attackers exploiting vulnerabilities within minutes.
- Cloud Complexity: 60% of cloud containers live for less than a minute, making periodic scans ineffective.
- Faster Detection: Companies using real-time systems report up to a 97% reduction in detection time.
- Reduced Noise: Prioritizing actionable risks cuts false alarms by up to 96%.
The key components of real-time threat intelligence include continuous data collection, automated threat detection, and instant responses. However, challenges like data volume, multi-cloud integration, and skills gaps require careful planning. Organizations that prioritize this approach can act faster, reduce risks, and stay ahead of attackers.
Real-Time Threat Intelligence Impact: Key Statistics and Benefits
Real-time Threat Intelligence Integration | Exclusive Lesson
sbb-itb-3b7b063
Why Real-Time Threat Intelligence Matters for Cloud Security
Cloud security demands a fresh approach compared to traditional methods. The fast-paced nature of cloud environments renders periodic scanning ineffective. Attackers often exploit vulnerabilities within hours of discovery, leaving scheduled scans unable to keep up.
Real-time threat intelligence closes this gap by instantly analyzing every API call and log entry instead of relying on delayed reviews. This approach is critical for implementing zero-trust security models, which operate on the principle of "never trust, always verify." Continuous verification relies on real-time context - such as who is making a request, what device they are using, and their typical behavior. Without this, enforcing zero-trust becomes nearly impossible. With real-time context, organizations can automate responses and secure their cloud environments more effectively and quickly.
The difference this makes is striking. Industry averages show attackers often remain undetected for weeks, but organizations using real-time detection reduce this window to just hours. For instance, in February 2026, companies using Cy5's "ion" cloud security platform reported a 97% reduction in Mean Time to Detect (MTTD) and a 96% drop in alert noise by shifting from traditional scanning to event-driven systems.
Beyond detection, automated remediation ensures threats are neutralized before they escalate. Real-time systems can revoke compromised credentials, rotate keys, or isolate affected resources immediately, cutting down response times and preventing widespread outages.
Benefits of Real-Time Threat Intelligence
The advantages of real-time threat intelligence span several areas of cloud security operations. One of the most immediate benefits is faster threat detection. Event-driven systems respond within seconds, drastically reducing the time attackers have to exploit vulnerabilities.
Another key improvement is reduced alert fatigue. Traditional systems often generate excessive false positives, overwhelming security teams. Real-time platforms, however, prioritize alerts based on actual risk in the specific environment. For example, Google's Detection and Response team automates 97% of security event analysis, allowing analysts to focus on high-risk scenarios that require human judgment.
Improved compliance and operational efficiency naturally follow continuous monitoring. Real-time platforms maintain detailed, timestamped records of all security events and responses, simplifying audits. In January 2025, Google's team saw a 53% reduction in time spent on incident executive summaries by using LLM-generated drafts. This freed up security staff to concentrate on investigations and preventive measures rather than manual documentation. Additionally, automated systems can retrieve telemetry and user data instantly, eliminating repetitive tasks that Tim Nguyen, Director of Detection and Response at Google, refers to as "toil".
Finally, better resource allocation becomes possible when security teams aren't bogged down by irrelevant alerts. By focusing on real-time data and actual threats, organizations can direct their resources toward the most pressing issues instead of chasing theoretical risks flagged by generic feeds.
Common Implementation Challenges
Despite its advantages, implementing real-time threat intelligence comes with challenges. Data volume and processing complexity are significant hurdles. Continuous streams from cloud control planes generate enormous amounts of data that need to be processed and analyzed without delays.
Integration across multi-cloud environments is another obstacle. Security teams often face "console toggling", where they switch between interfaces like AWS, Azure, and GCP to piece together a complete picture. Differing log formats, API structures, and naming conventions make achieving unified visibility a technical challenge.
Alert quality and context also remain problematic. Tim Nguyen highlights this issue:
"If you're not in charge of engineering an alert, do you care if it fires off at 3:00 in the morning?".
This points to a disconnect between those who write detection rules and those who handle the alerts. Google's "You Write It, You Triage It" policy addresses this by ensuring engineers who create alerts are also responsible for triaging them.
The skills gap is another barrier. Real-time threat intelligence platforms require teams with expertise in both cloud architecture and threat analysis. Unfortunately, 82% of security and IT leaders believe their organizations might be missing cyberattacks, and 72% describe their cybersecurity posture as "mostly reactive". This lack of skilled personnel limits the ability to fully leverage real-time systems.
Finally, automation boundaries must be carefully managed. Deciding which responses can be automated and which require human intervention is tricky. Automating everything risks disrupting legitimate operations, while automating too little undermines the purpose of real-time detection. The solution lies in using risk-encoded runbooks: automating low-risk actions while routing high-stakes decisions through human review.
| Challenge | Impact | Mitigation Strategy |
|---|---|---|
| Data Volume | Lag and storage overhead | Sharded, edge-based architectures with fast queries |
| Multi-Cloud Integration | Fragmented visibility and "console toggling" | Unified platforms normalizing schemas across clouds |
| Alert Fatigue | Analyst burnout and missed threats | Context-aware prioritization and triage policies |
| Skills Gap | Underutilized capabilities | Training programs and AI-assisted tools |
| Automation Risk | Potential business disruption | Risk-encoded runbooks with human oversight |
Core Components of a Real-Time Threat Intelligence System
An effective threat intelligence system takes raw data and turns it into actionable defenses in real time.
Centralized Data Collection and Correlation
The first step in any real-time threat intelligence system is gathering data from a variety of sources. These include internal network logs, open-source intelligence (OSINT), commercial threat feeds, dark web monitoring, and cloud API telemetry. However, the real challenge isn’t just collecting this information - it’s making sense of it. Data from these sources often comes in different formats, and duplicates are common. To make this data useful, it must be normalized and cleaned up.
Jerome Clauzade from CrowdSec highlights why this step is so critical:
"The quality of the data collected at this stage will define all the following stages. With low-quality, inaccurate, or undiversified data, the subsequent analysis will produce inaccurate results".
Automation plays a key role here. Systems can normalize data using formats like STIX, handle multilingual sources, process encrypted data, and eliminate duplicates. Once the data is cleaned, it’s correlated to uncover patterns that might not be obvious from isolated alerts. For example, a single suspicious IP address might seem unimportant on its own. But when combined with passive DNS data, geolocation information, and behavioral patterns, it could reveal a larger attack campaign. This process of contextual enrichment transforms raw indicators into meaningful insights, breaking down information silos and cutting down on false positives.
Machine learning further refines this process by filtering out noise, allowing analysts to focus on the most critical alerts. With enriched and correlated data in hand, organizations are better equipped to detect threats quickly and accurately.
Automated Threat Detection and Response
Detecting a threat is only half the battle - responding immediately is just as important. Tools like SIEM and SOAR platforms can automate responses, such as blocking malicious IPs, revoking compromised credentials, or isolating affected systems. Risk-based workflows can determine when human intervention is necessary, ensuring a balance between automation and oversight. Features like dynamic access controls, Just-in-Time provisioning, and automated containment workflows limit an attacker’s ability to move laterally within a network.
Automation is particularly crucial for zero-trust architectures, which operate on the principle of "never trust, always verify." Aparna Achanta, Principal Security Architect at IBM, explains:
"AI strengthens zero-trust security principles by automating processes with greater accuracy and speed than humans".
By aligning with zero-trust principles, automated systems ensure that responses are both fast and effective, minimizing disruption while maintaining security.
Post-Incident Analysis and Improvement
Once an incident is detected and contained, the next step is learning from it. Post-incident analysis helps refine defenses for the future. Retrospective analysis, for example, can apply new indicators of compromise (IOCs) to historical logs, revealing threats that might have gone unnoticed before.
A structured feedback loop is essential for continuous improvement. Following a defined intelligence lifecycle - Planning, Collection, Processing, Analysis, Dissemination, and Feedback - ensures that threat intelligence remains aligned with the organization’s evolving risk landscape. This approach helps organizations move from a reactive stance (where 72% currently find themselves) to a more predictive and proactive posture. Insights gained during this process feed back into the data collection phase, creating a self-reinforcing cycle that strengthens defenses over time.
| Component | Primary Function | Key Technologies |
|---|---|---|
| Data Collection | Aggregate raw indicators from multiple sources | AlienVault OTX, MISP, AbuseIPDB |
| Enrichment | Add context, such as reputation and ownership | VirusTotal, GreyNoise, Shodan |
| Correlation | Link indicators to specific campaigns | OpenCTI, TheHive, Microsoft Sentinel |
| Automation | Trigger workflows and auto-blocking | Cortex, Shuffle, Splunk SOAR |
| Standards | Ensure data interoperability | STIX, TAXII |
Best Practices for Integrating Real-Time Threat Intelligence
To get the most out of real-time threat intelligence, it's crucial to focus on clear metrics, smart automation, and a commitment to ongoing improvement. Success in this area relies on aligning people, processes, and technology seamlessly.
Set Clear Goals and Metrics
Start by defining what success looks like. Establish Service Level Objectives (SLOs) to minimize attacker dwell time. Track actionable metrics like Mean Time to Detect (MTTD), Mean Time to Contain (MTTC), and your True Positive Rate. For example, organizations leveraging event-driven cloud security platforms have reported up to a 97% reduction in MTTD and a 96% drop in alert noise.
Avoid vanity metrics that don't drive real improvement. John Barth, Global Service Lead at Mandiant Intelligence Program Development, underscores the importance of a thoughtful and integrated approach:
"By thoughtfully investing in and harmonizing its people, processes, and technology, organizations can build a CTI program that not only identifies cyber threats but delivers actionable security recommendations".
Once goals are clearly defined, automating detection and response becomes the natural next step.
Automate Detection and Response
Streamline the parse-enrich-correlate cycle by normalizing data into a common schema early in the process. This eliminates redundant tasks and allows downstream tools to focus on analysis instead of re-parsing data. Integrating your Threat Intelligence Platform (TIP) with SOAR tools enables automated, rule-based alert handling.
A real-world example of automation at scale comes from Google's threat detection and response team. In January 2025, under the leadership of Tim Nguyen, the team automated 97% of security events using advanced "hunts", cutting threat dwell time from weeks to hours. They also introduced generative AI to draft executive summaries, reducing engineers’ writing time by 53% while maintaining accuracy. Tim Nguyen explains their guiding principle:
"Our motto is less gathering, more direct analysis. We believe people are uniquely good at understanding nuance, making judgments, and navigating ambiguous information. We want to augment building context as much as possible to give our team more time to make the right decisions".
Adopt a "human-in-the-loop" approach where machines handle repetitive, high-volume tasks while humans focus on complex, nuanced decisions. Automate low-risk remediations, but keep human oversight for high-impact actions that could affect critical operations.
Once automation is in place, regular audits and training ensure the system stays effective and adaptable to new threats.
Perform Regular Audits and Training
Routine audits are essential to prevent system inefficiencies. For instance, automating the expiration of outdated Indicators of Compromise (IOCs) can significantly reduce noise - some organizations find that up to 30% of their active IOCs are no longer relevant.
Engage directly with your SOC, incident response, and vulnerability management teams to identify their pain points before building or updating intelligence feeds. This ensures your system addresses real-world challenges rather than theoretical concerns. It's worth noting that 82% of security and IT leaders worry they may be missing cyberattacks, and 72% describe their approach as "mostly reactive". Regular training and audits help shift this mindset, empowering teams to move toward a more proactive defense strategy that evolves with emerging threats and techniques.
How Kanu AI Enhances Threat Intelligence

Securing cloud infrastructure requires automation, ongoing validation, and constant visibility. Kanu AI tackles these challenges by embedding security and observability directly into the software delivery process. This seamless integration builds on the real-time threat intelligence framework previously discussed.
Automated Infrastructure Code Generation
Kanu's Intent Agent transforms product requirements into secure, production-ready code. From the outset, the platform creates configurations with built-in security enhancements, aligning with the "Detection as Code" approach. This mindset treats security logic as a core part of software engineering rather than an afterthought. By automating infrastructure provisioning with pre-configured security guardrails, organizations can deploy threat intelligence capabilities more efficiently.
Built-In Validation and Compliance
Once deployed, Kanu runs over 250 validation checks on live systems to confirm that configurations adhere to security best practices and compliance standards like SOC 2 Type II. This approach replaces periodic audits with real-time monitoring, enabling instant detection of misconfigurations. Kanu also provides a complete audit trail with rollback options, ensuring every change is both traceable and reversible. By treating configuration changes as immediate signals rather than waiting for scheduled scans, Kanu significantly reduces the time attackers have to exploit vulnerabilities.
After securing the deployment, Kanu AI continues to monitor live systems, delivering insights that organizations can act on immediately.
Real-Time Insights from Logs and Metrics
Kanu continuously processes logs and metrics from deployed applications, offering actionable insights that speed up threat detection and response. Its DevOps Agent and QA Agent collaborate to pinpoint anomalies, troubleshoot issues, and recommend fixes - whether it's a Terraform adjustment, a policy revision, or a CLI script. With zero data egress by default and a single-tenant architecture operating within user-defined boundaries, Kanu ensures that sensitive data stays within your environment while still delivering the speed and automation required for modern threat intelligence.
Conclusion
Cloud breaches no longer unfold slowly - they happen in real time. Attackers exploit vulnerabilities within minutes, and ransomware typically executes in just five days on average. For organizations relying on periodic scans and reactive recovery plans, this pace leaves them dangerously behind. As Sergiy Balynsky, VP of Engineering at Spin.AI, puts it:
"The organizations winning this fight aren't the ones with the best recovery plans. They're the ones who see the attack forming and stop it before encryption begins."
The key to staying ahead lies in real-time threat intelligence, which transforms raw data into immediate, decisive action. Sub-second detection, behavioral modeling, and event-driven systems that analyze every API call are no longer optional - they're essential. In fact, the percentage of ransomware attacks stopped before encryption jumped from 22% in 2023 to 47% in 2025, proving that proactive defenses save the day when systems operate at machine speed.
This shift demands integrated solutions that embed security into every stage of delivery. While automated systems handle 97% of events, human expertise remains critical for high-stakes decisions. Platforms like Kanu AI exemplify this balance by automating infrastructure provisioning with built-in guardrails, conducting over 250 live system validation checks, and offering actionable insights from logs and metrics - all while ensuring sensitive data stays within your environment.
With ransomware attacks surging by 149% year-over-year and 82% of leaders worried about missed cyber threats, the need to move from reactive to proactive security has never been more urgent. The time to act is now.
FAQs
What’s the difference between real-time threat intelligence and periodic scanning?
Real-time threat intelligence works by constantly gathering and analyzing data to spot potential attacks as they happen. This approach allows for quick detection and response, reducing the time threats linger and lowering the chances of them escalating into bigger issues.
In contrast, periodic scanning happens on a set schedule - like daily or weekly. While it can uncover vulnerabilities, it only does so after the fact, creating windows of time where threats might slip through unnoticed.
Which responses should be automated vs. require human approval?
Automated responses are great for tackling straightforward tasks. They can handle things like updating security rules, blocking malicious traffic, or tweaking firewall settings - all in real time. This ensures threats are addressed quickly, without unnecessary delays.
However, when it comes to more complex or unclear situations, human oversight is crucial. For example, analysts step in to handle ambiguous threats, make policy decisions, or evaluate potential false positives. They validate the automated actions, review alerts, and analyze the broader context to ensure accuracy and prevent unnecessary disruptions.
How can you unify threat data across AWS, Azure, and GCP in real time?
To bring together threat data from AWS, Azure, and GCP in real time, consider using an event-driven security architecture. This approach treats security events as actionable signals, enabling automated responses. Leverage cloud-native tools like AWS Lambda, Azure Sentinel connectors, and Google Cloud threat detection systems to ingest and correlate data effectively. By centralizing these feeds in a SIEM or orchestration layer, you can achieve real-time detection and response across your multi-cloud setup.